The knowledge contained in the minds of staff in any dental office is immense. Dental anatomy and physiology, general health and welfare, cleaning, x-rays, prepping, billing, customer service. The list goes on. Many procedures and protocols make an office run smoothly and efficiently.
On top of everything else, it is critical to take steps to keep your digital world secure and your patients’ information safe-guarded. Nothing will stop business faster than malicious software that takes over your network. Someone could steal your office’s financial information, protected patient health information, and log-in credentials for numerous websites.
To dramatically reduce the risk of an attack, take these five steps today:
Ensure each user has a unique log-in
Passwords are a pain, but they are vital. Enforce a strong 10-character minimum password policy. You are probably familiar with password requirements for most websites: upper- and lower-case letters, numbers, and a special character. And although the address of your office meets those requirements, it does not make for a secure password. Nor do such easily guessed ones as Dental/22 and Teeth123$.
Along with the unique password, each user should only use a computer in which they have entered their unique credentials. When you are leaving your computer, lock it (Windows key + L) so no one can use the station as YOU. Logs are created that show when each person is logged into each computer and might be used to trace a leak of PHI (Protected Health Information). A patient has the right to a list of those who have accessed their PHI, when it was accessed, and for what it was used.
Implement a schedule to change and update passwords during each year. Once a year at a minimum for password changes should be sufficient and not difficult for your employees. Also, make sure no passwords or any form of log-in credentials are posted or visible around the office.
Always call and verify when you get an email with attachments you were not expecting
It is routine to send and receive additional documentation from patients, insurance companies, or specialty offices on a regular basis. Many offices, to reduce paper waste and clutter, have made efforts to make this additional documentation completely digital. Email and fax services will create PDFs that can be easily viewed and stored for later. This opens offices to malicious attacks through software embedded in attachments.
Follow simple rules to keep your network and patient PHI safe:
1. If you are not expecting it, do not open the attachment.
2. If you do not recognize the sender, do not open the attachment.
3. If there are obvious grammar and spelling errors in the email, do not open the attachment.
Take time to reach out to the sender by phone or by a separate email, to ask what was sent. Or log into your online account for that insurance company to see if messages or documents are waiting for you. Their websites are secure for the exchange of information. Email is not a secure means of sending PHI.
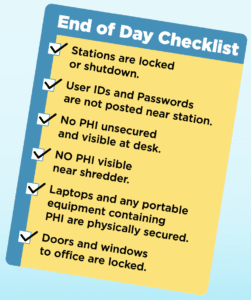
End of day security checklist
Your office can take a vital step to secure patient PHI with a simple checklist, to be completed each day. It can identify staff members who need additional training on HIPAA and provide instruction as to how to secure PHI. By using a daily checklist, you establish a history of standard office procedures for digital security which can help if there is ever a question about how your office handles sensitive information.
Keep your operating system up-to-date
Check regularly for any updates. If you have an outside company that takes care of your computers, verify they are keeping up with the latest updates and securing your regular back-up of data.
If you are responsible for the computers, you can check for updates on a PC by simply typing “check for updates” in the search box at the bottom left of your screen.
Then click the Check for updates shortcut that appears.
![]()
Remember to back up office data regularly. Your practice management system may have a routine for backing up the information saved inside your program. Call your support team to confirm instructions for running and securely saving the information.
Secure or shred any hard copies that contain PHI
Printouts and forms from insurance companies identify the insured person so you know to which patient the correspondence refers. Notes you make when talking to an insurance company might have social security numbers, subscriber IDs, dates of birth, and descriptions of procedures on them. Do you use a hard copy form for your insurance verification? All of that is PHI and needs to be secured when you are away from your station. Turn the pages over, put them in a drawer, and be sure they are shredded when you are finished.
There are plenty of resources regarding HIPAA compliance including programs, books, seminars, and consultants. You can find a consultant or company that specializes in compliance for the dental field. If you contract with a company for your human resources, ask about employee training videos. YouTube has videos that explain HIPAA and best practices to be compliant. Document all training: who was there, how much time was spent, and what was the topic. You can put together a simple list for onboarding new employees and keep records of your efforts to be compliant.
Corey Murillo has been Director of IT at Trojan Professional Services since 2016. He is directly responsible for Trojan attaining and maintaining EHNAC Accreditation.
FMI: www.ehnac.org
Nikki Myers is the Marketing Coordinator for Trojan Professional Services and has been the Publishing Coordinator for Trojan Today since 2018.
Read more from Nikki:

